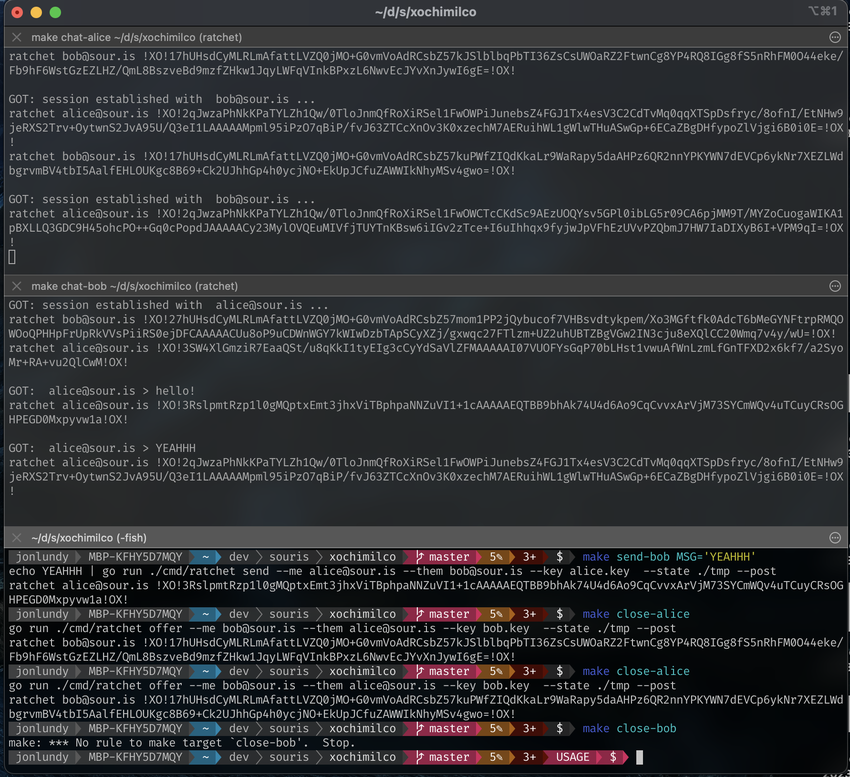
I spent the day today integrating @xuu@txt.sour.is’s double ratcheting work and ratchet library back into the reference client/broker implementation saltyim as a v2 branch. I completely redesigned and rewrite the salty-chat TUI client as well, which now includes proper notifications and a background agent that keeps running so you never miss any messages. It all “just works”™ and I’m quite happy with the outcome! 🤩 #saltyim #revamp
ProcessOne: On Signal Protocol and Post-Quantum Ratchets
Signal improved its protocol to prepare encrypted messaging for the quantum era.
They call the improvement “Triple Ratchet” (or SPQR = Signal Post-Quantum Ratchet).
[Signal Protocol and Post-Quantum Ratchets\ \ We are excited to announce a significant advancement in the security … ⌘ Read more
(#2s7hrha) @eapl.me Yeah this is true. Previously RSA and AES were more common. These days Salsa and Chacha and Curve are fairly prevalent. For …
@eapl.me @eapl.me Yeah this is true. Previously RSA and AES were more common. These days Salsa and Chacha and Curve are fairly prevalent. For example all the Wireguard stuff uses Curve25519 / Ed25519 crypto. Signal uses very similar crypto too, but with some very nice double ratcheting 3DH. ⌘ Read more
@lyse@lyse.isobeef.org I have read the white papers for MLS before. I have put a lot of thought on how to do it with salty/ratchet. Its a very good tech for ensuring multiple devices can be joined to an encrypted chat. But it is bloody complicated to implement.
@lyse@lyse.isobeef.org I have read the white papers for MLS before. I have put a lot of thought on how to do it with salty/ratchet. Its a very good tech for ensuring multiple devices can be joined to an encrypted chat. But it is bloody complicated to implement.
And to add close integration with salty/ratchet for realtime private chat
And to add close integration with salty/ratchet for realtime private chat
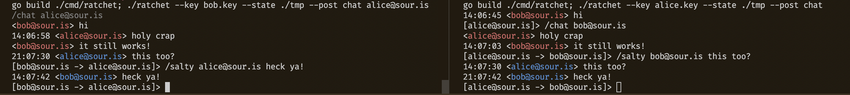
Ratchet CLI now supports salty or ratchet comms!
Ratchet CLI now supports salty or ratchet comms!
ChatGPT is good, but it’s not that good 🤣 I asked it to write a program in Go that performs double ratcheting and well the code is total garbage 😅 – Its only as good as the inputs it was trained on 🤣 #OpenAI #GPT3